User verification check results
On the Verification tab, you can review statistics on user verification (KYC).
The statistics includes a comprehensive summary of the verification process, it also displays the related events that represent the sequence in which applicant profiles were processed, webhooks sent during verification, workflows that have been involved in the verification process, identity and address verification results, and many other.
NoteNot all sections described below may be available, as it depends upon the verification level settings and checks passed by the applicant.
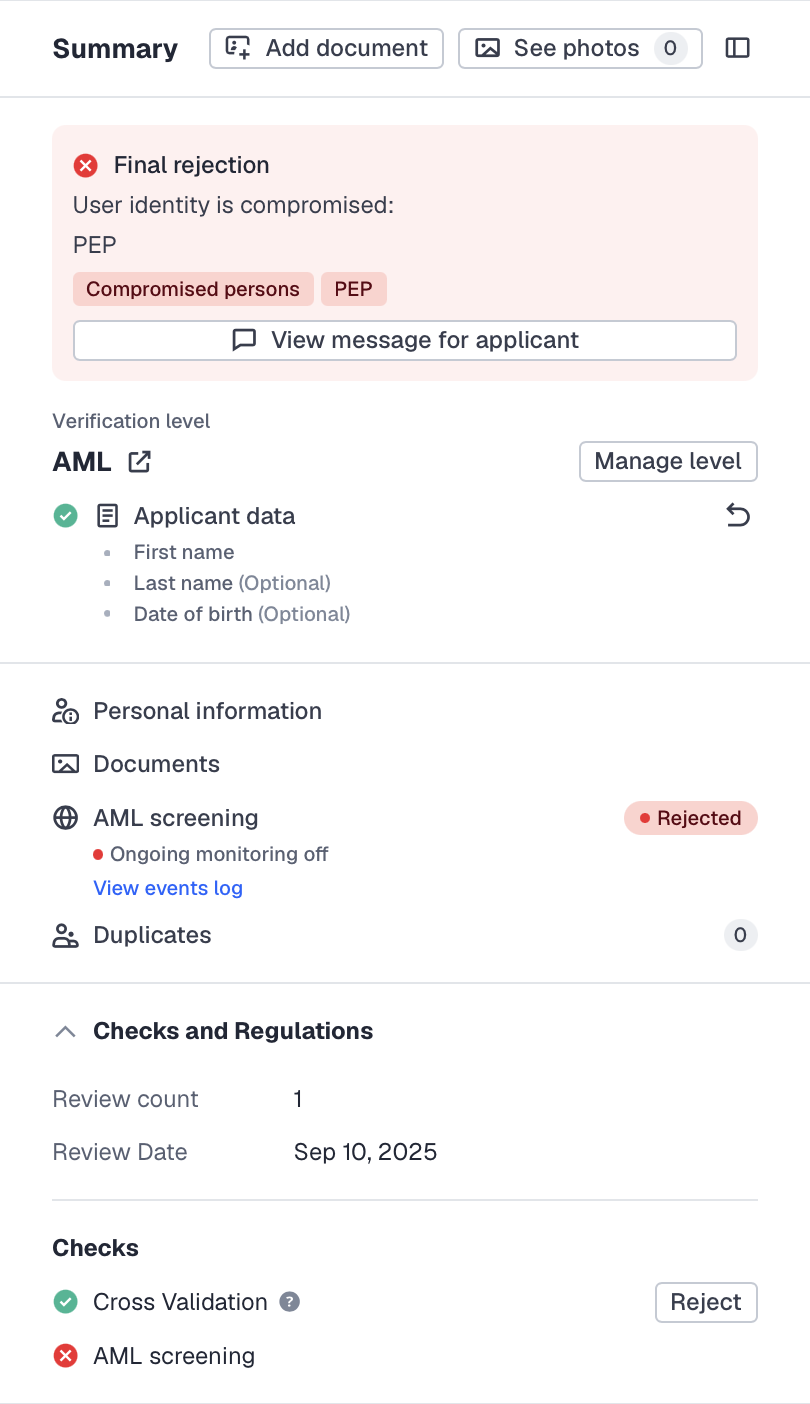
Summary
Summary provides you with the core information about the applicant level and allows you to quickly navigate through the completed steps, checks, and regulations.
NoteFor rejected applicants, we also display the type of rejection and explanatory buttons adding a context about a rejection reason.
To see the full list of rejection reasons, refer to this article.
In this section, you can also manage the current verification level. For more information on how to create and edit verification levels, see this article.
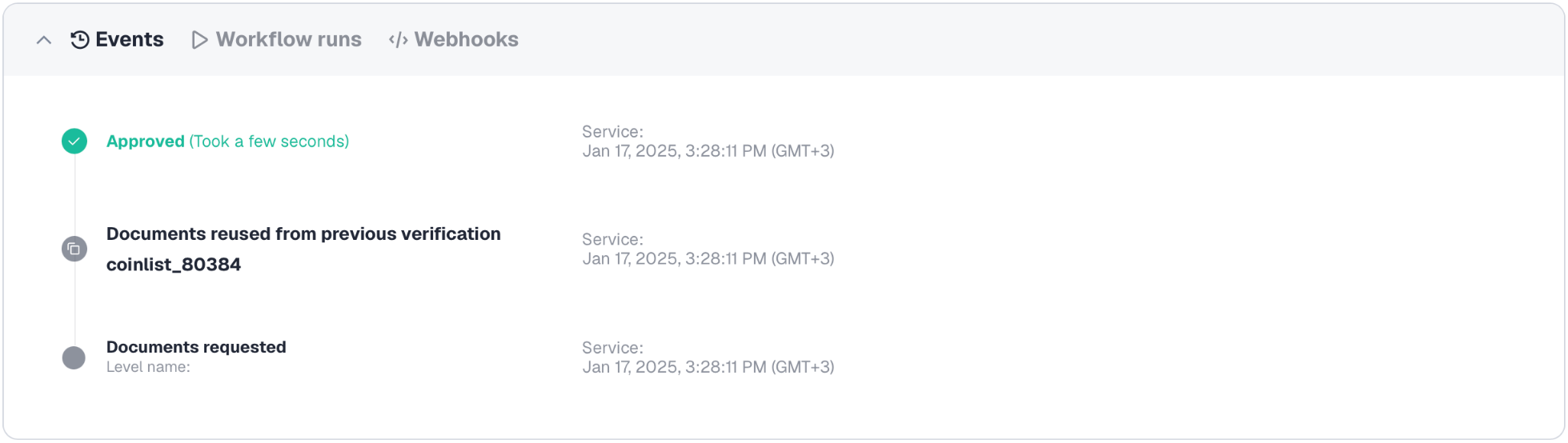
Events
Events show the sequence in which applicant profiles are processed. For example, each time an email or SMS is sent to the applicant, a new document is uploaded, the applicant is declined or approved, and so on, a dedicated event is saved and displayed as a reference. You can also view the applicant creation date along with who has changed applicant or document status.
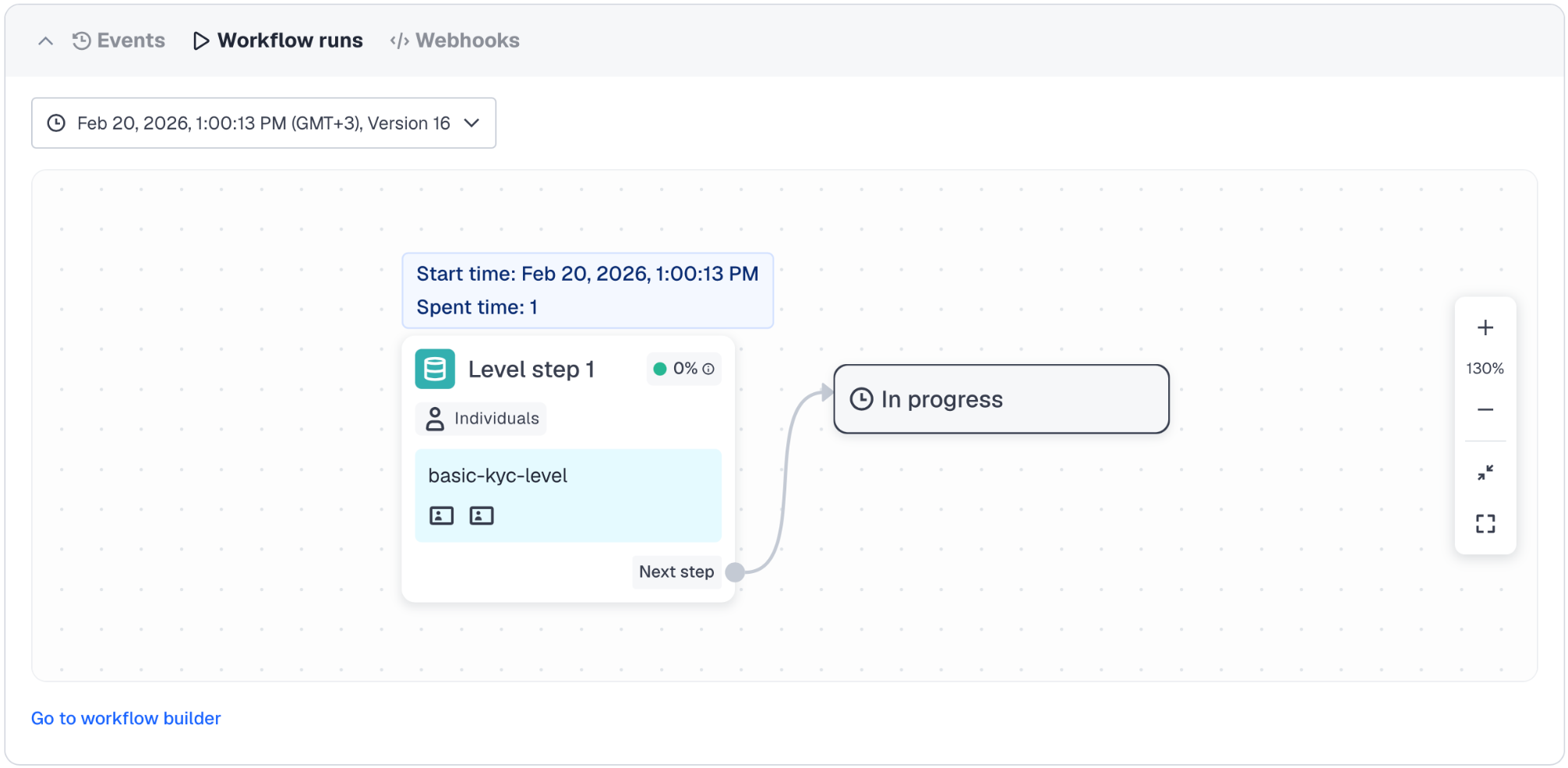
Workflow runs
The Workflow runs tab shows the applicant’s verification journey, including all completed steps and their current status. This helps track where the applicant is in the process, as long as they belong to a workflow. For more information on Workflow Builder, see this article.
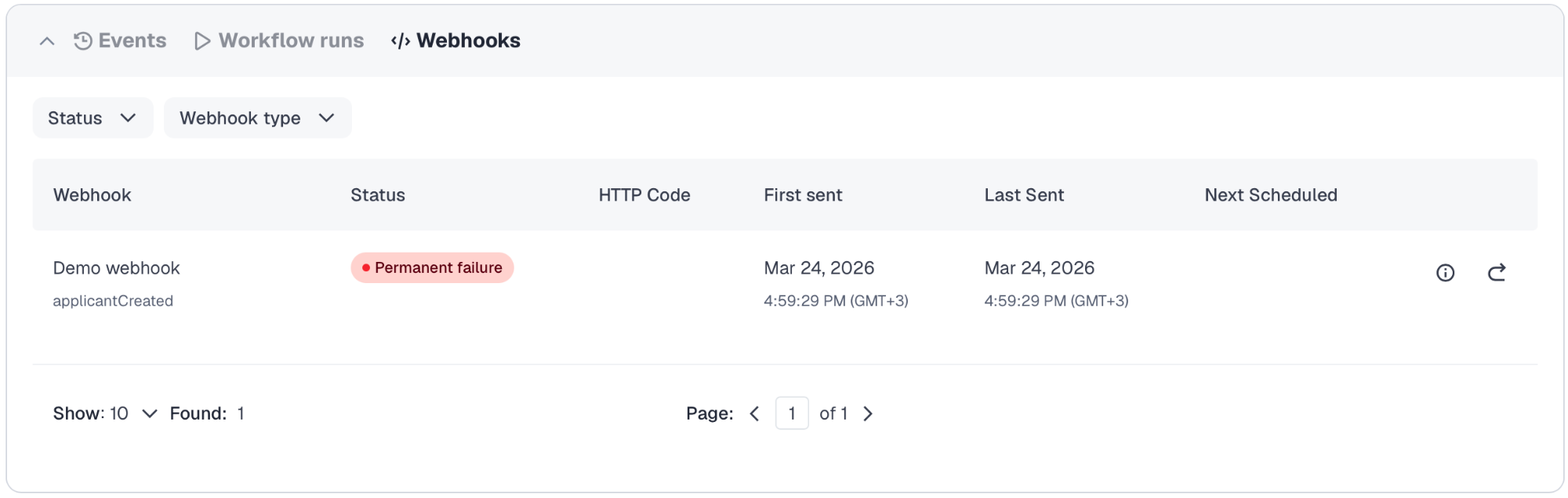
Webhooks
The Webhooks tab displays all webhooks sent for that specific applicant with its details, including type and status, and the option to resend it if needed. For more information on webhooks, see this article.
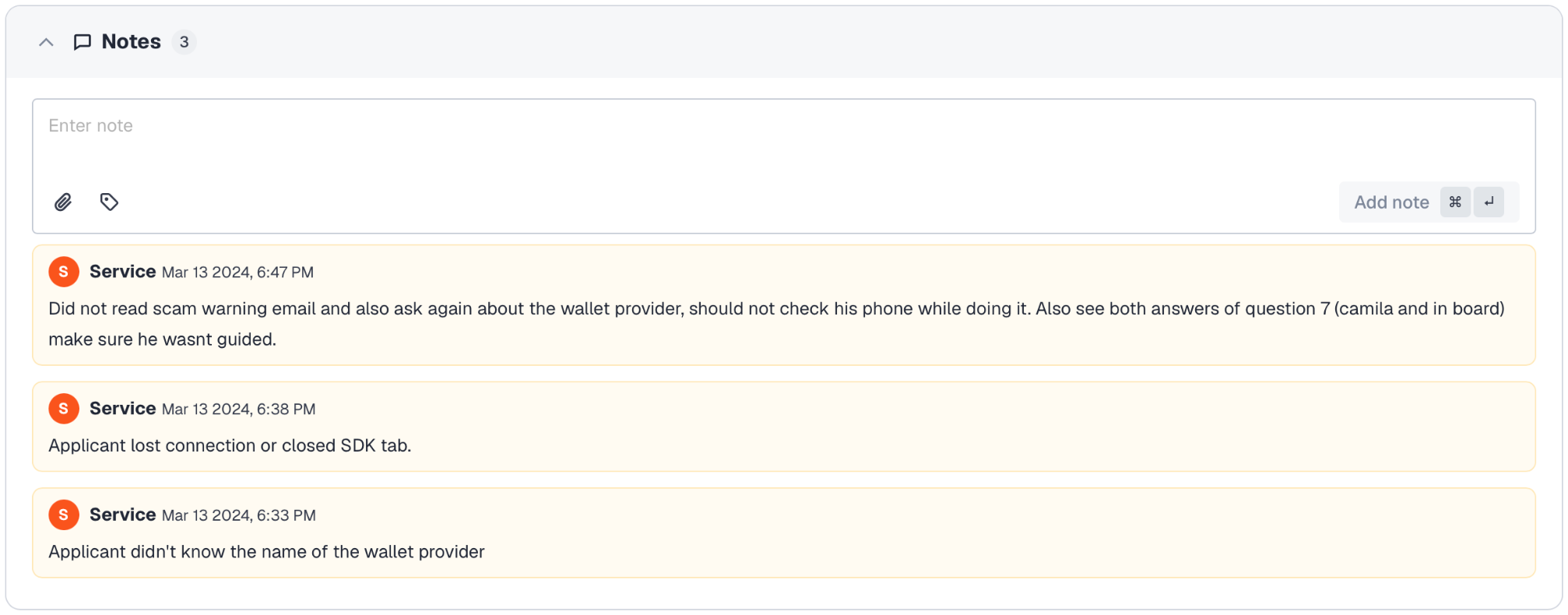
Notes
Notes help you preserve and share information (or memos) that you or Sumsub operators may have saved to emphasize important aspects related to the given applicant. For example, when we decline an applicant as a possible PEP, and you decide to approve this applicant, you can let us know about your decision by leaving a note.
Tags and file attachments can also be added to a note to provide context and supporting information.
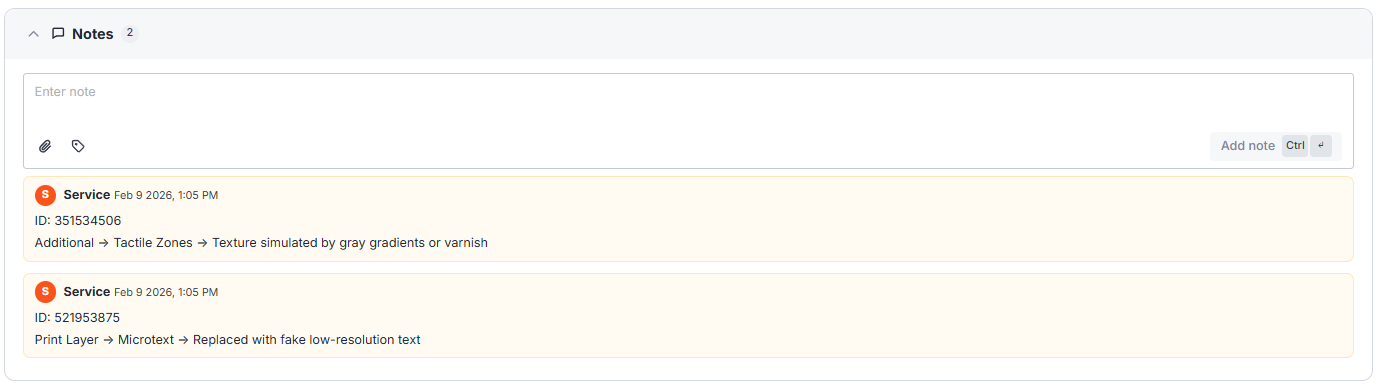
Fraud segmentation notes
Fraud segmentation notes are system-generated records stored in the Notes section to provide an additional layer of information regarding rejection reasons. Each note includes the following information:
- Identification number of modified image (video)
- Fraud type (category)
- Affected security features
- Alteration characteristics
Note
- Fraud segmentation notes are visible only to Dashboard users with the Admin role.
- You can edit and delete fraud segmentation notes, but you cannot assign them to applicant profiles manually.
Below you can find detailed information on each fraud category, outlining the associated security features, applicable document types, and specific signs of alteration.
Print Layer
Print layer fraud refers to various techniques used to imitate advanced printing-based security features.
Expand to review a lisf of print-layer security features and associated fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Microtext |
|
|
|
Guilloche Patterns |
|
|
|
Micro-images / Hidden Graphics |
|
|
|
Optically Variable Ink (OVI) |
|
|
|
UV / IR inks |
|
|
Material
Material fraud involves the falsification or replacement of the document’s base material and integrated security components, compromising structural and physical authenticity.
Expand to review a list of material security features and associated fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Polycarbonate / Laminated Layers |
|
|
|
Embedded Fibers / Security Threads |
|
|
|
Laser / Tactile Perforation |
|
|
|
Laser Engraving / Embossing |
|
|
Optical
Optical fraud targets the visual or light-responsive security elements of documents.
Expand to review a list of optical security features and associated fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Holograms / Kinegrams |
|
|
|
Ghost Image / Secondary Portrait |
|
|
|
Transparent Window |
|
|
Electronic
Electronic fraud involves various manipulations aimed at falsifying digital and machine-readable security features.
Expand to review a list of electronic security features and associated fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
MRZ |
|
|
|
NFC Chip |
|
|
|
Barcode / QR Code |
|
|
Additional
Additional fraud refers to mixed manipulations targeting supplementary security mechanisms.
Expand to review a list of additional (mixed) security features and associated fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Tactile Zones |
|
|
|
Register Printing |
|
|
|
Latent Image |
|
|
|
Fluorescence (UV) |
|
|
|
Serial Numbers |
|
|
|
Font mismatch |
|
- |
Edited data
The Edited data category identifies the specific personal data points to which alterations have been applied.
Expand to review a list of edited data points identified by the system.
|
Alteration characteristics |
Document types |
|---|---|
|
|
|
|
|
Payment methods |
|
Selfie + PoI |
Deepfake
Deepfake refers to AI-generated or synthetically manipulated facial imagery or video used to falsify identity.
Expand to review a list of deepfake features and associated fraud indicators identified by the system.
|
Affected feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Face and Skin |
Selfie |
|
|
Eyes |
Selfie |
|
|
Mouth and Speech |
Selfie |
|
|
Lighting and Background |
Selfie |
|
|
Indirect Indicators of Identity Forgery |
Selfie |
|
Proof of address
The Proof of address category identifies the specific PoA document data points to which alterations have been applied.
Expand to review a list of PoA fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Layout & Format |
PoA (bill) |
|
|
Image Quality |
PoA (bill) |
|
|
Laser / Tactile Perforation |
PoA (PoI as PoA) |
|
|
Data inconsistencies |
PoA (bill) |
|
Templates
Template refers to a common document format or layout (such as structure, fonts, and visual elements) typically used for a specific document type. Submitted documents are compared against a database of these formats.
Expand to review a list of templates-related fraud indicators identified by the system.
|
Affected security feature |
Document types |
Alteration characteristics |
|---|---|---|
|
Layout Uniformity |
PoA (bill) |
|
|
Background / texture |
PoA (bill) |
|
|
Document generation logic |
PoA (bill) |
|
|
Transaction or billing structure |
PoA (bill) |
|
|
Bank card design |
Payment methods |
|
|
Suspicious document |
PoI, PoA (bill + PoI as PoA), Selfie |
|
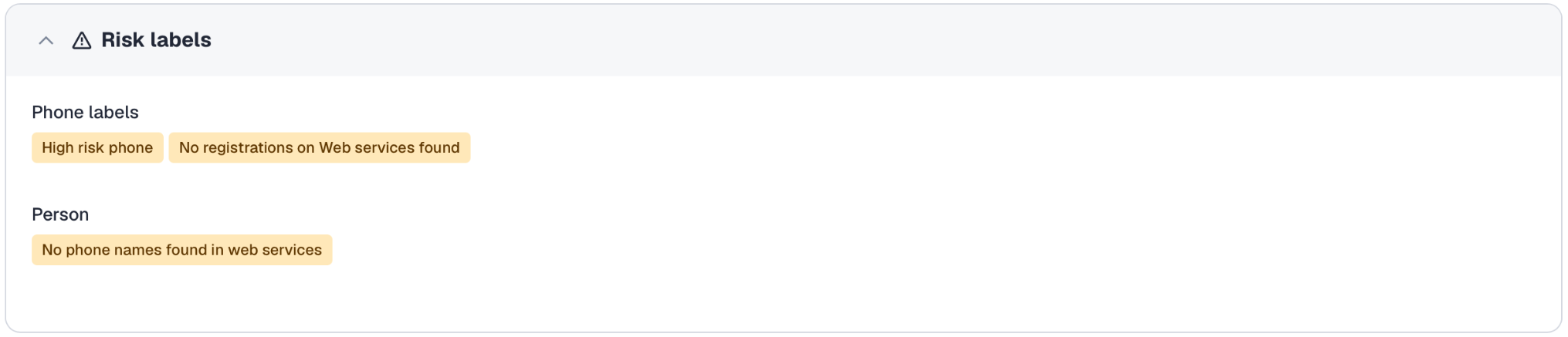
Risk labels
Risk labels are assigned during verification and indicate certain characteristics of an applicant. For more information, see this article.
Applicant information
The Applicant information section contains the applicant’s personal details, provided information, and data extracted from uploaded documents.
Additional documents can also be uploaded here if needed.
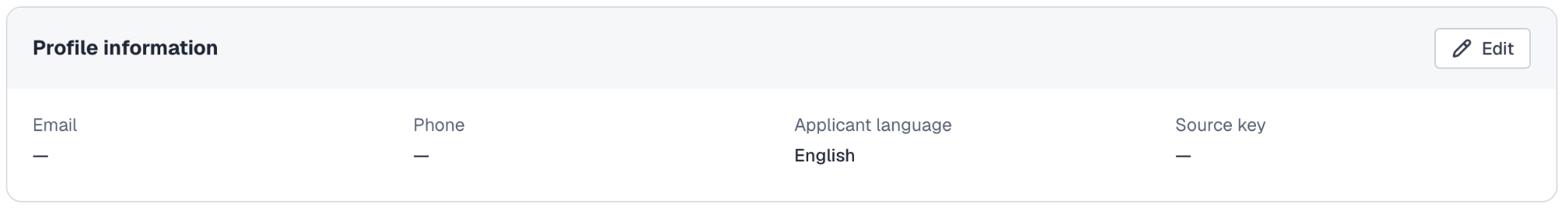
Profile information
The Profile information shows top-level applicant details, such as applicant email address, phone number, language, and source key. You can change or update this information at any time.
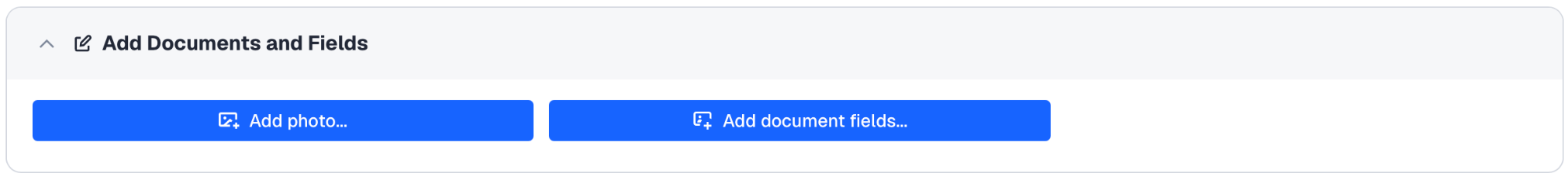
Add Documents and Fields
In this section, you can manually upload additional documents or add other document fields with information needed during the applicant’s verification process. For example, when performing a manual check or running Video identification. Documents that are not used for verification can also be added to enrich the applicant’s profile. For more information on how to add documents, refer to this article .
Personal info
These sections show the following:
- Extracted information — displays the information recognized and extracted from the applicant documents. It is updated automatically when document data is changed.
- Provided information — displays the information submitted by the applicant via the WebSDK or MobileSDK or via this API method.
- Address — displays address information collected during verification:
- Extracted from the applicant's PoA documents.
- Submitted by the applicant via the WebSDK and MobileSDK.
You can also submit this information using this API method.
Documents
Documents displays the applicant’s identity documents and the information automatically extracted from them. If the verification includes a questionnaire, the submitted answers are shown here as well.
Here, you can also:
- Add documents to the applicant by selecting its type and country and uploading the file.
- View all document files with its data in one tab by clicking See photos.
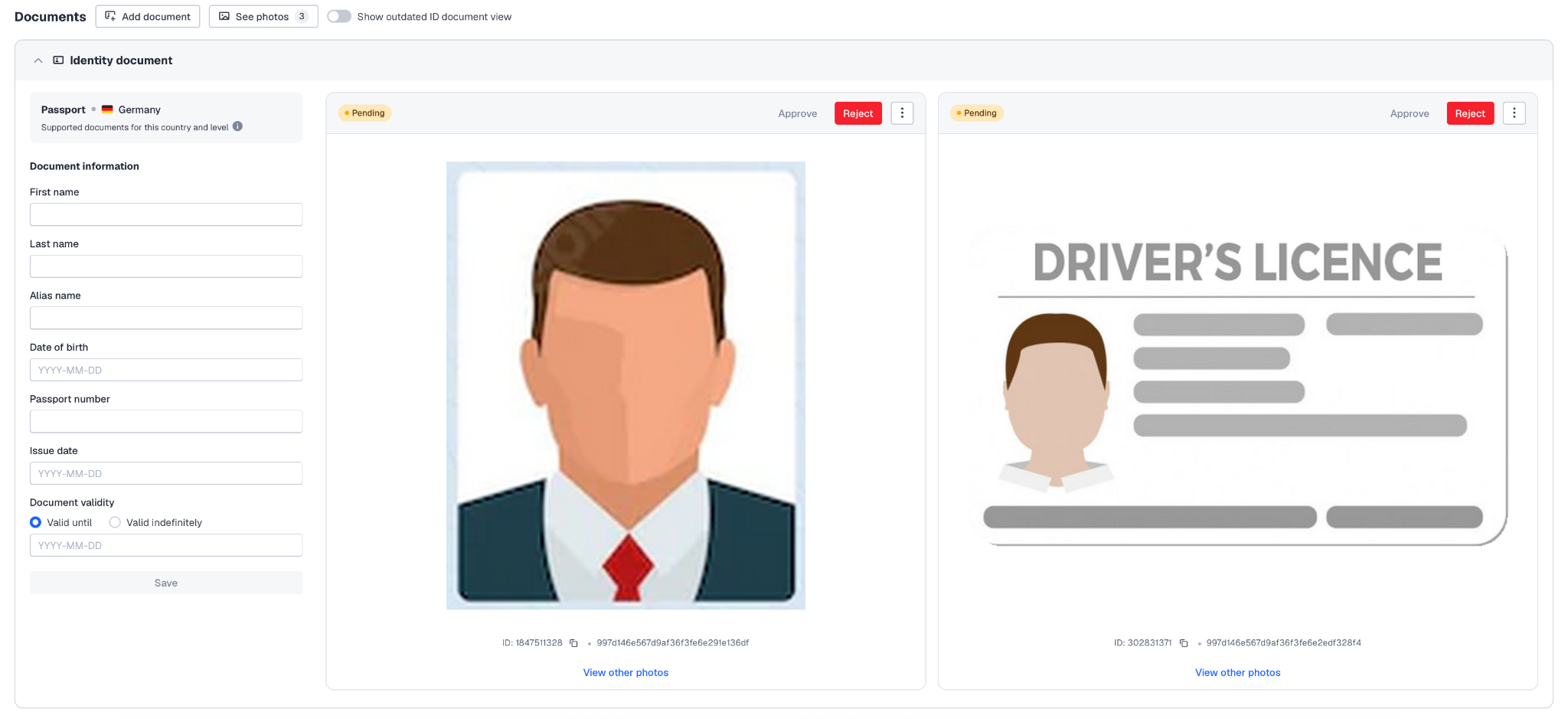
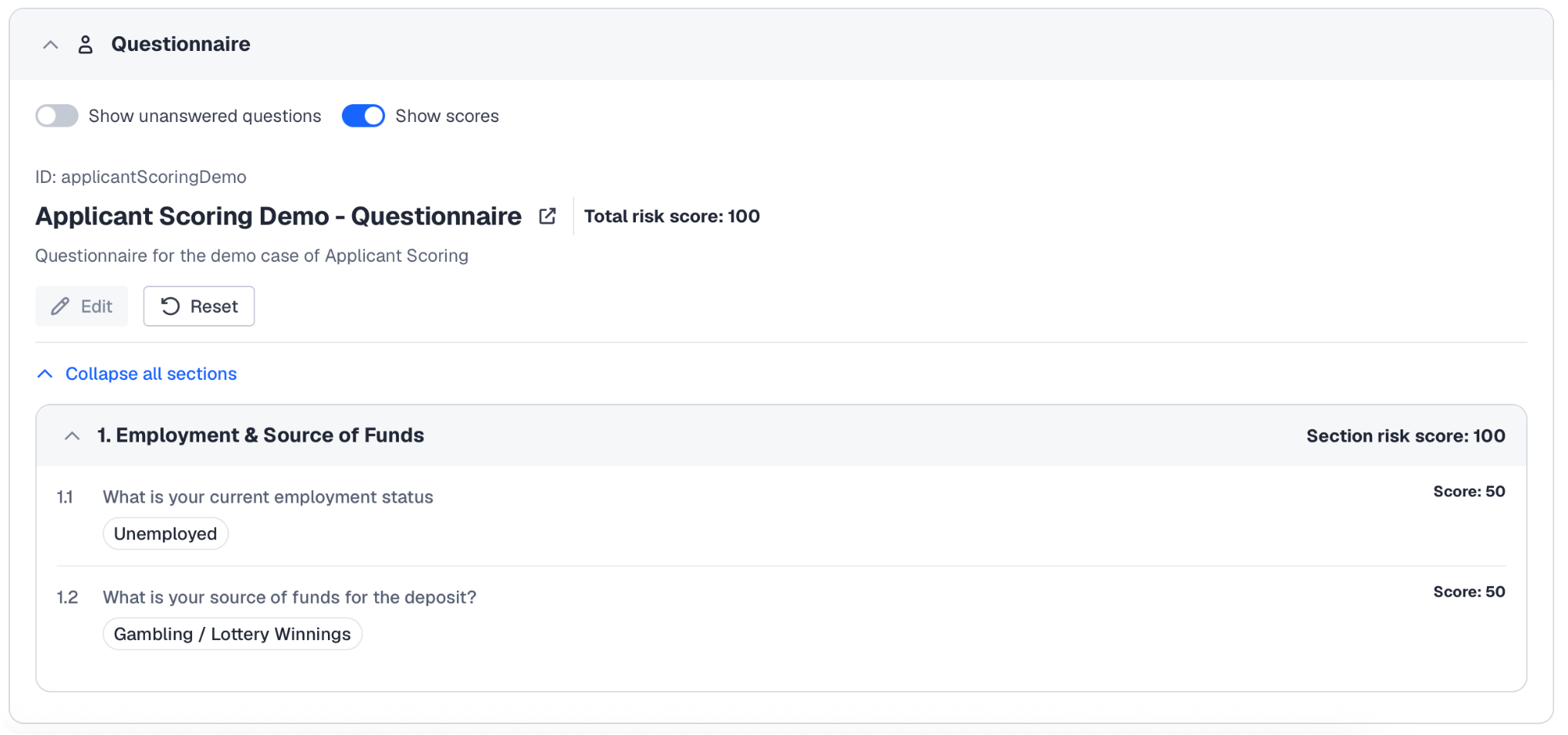
Questionnaire
The Questionnaire section shows a questionnaire required to be completed by the applicant during or after verification. An operator who runs a video identification can also complete the questionnaire using the answers provided by the applicant.
After the questionnaire is complete, you can find the submitted answers and uploaded files in the Questionnaire section.
To resubmit the information for a completed questionnaire, you can reset the questionnaire by clicking Reset. Alternatively, you can use this API method providing the
QUESTIONNAIREparameter.
Checks
The Checks section includes the results of all checks required for verification, such as identity data and proof of address checks, email and phone confirmation, and other checks depending on the current verification level.
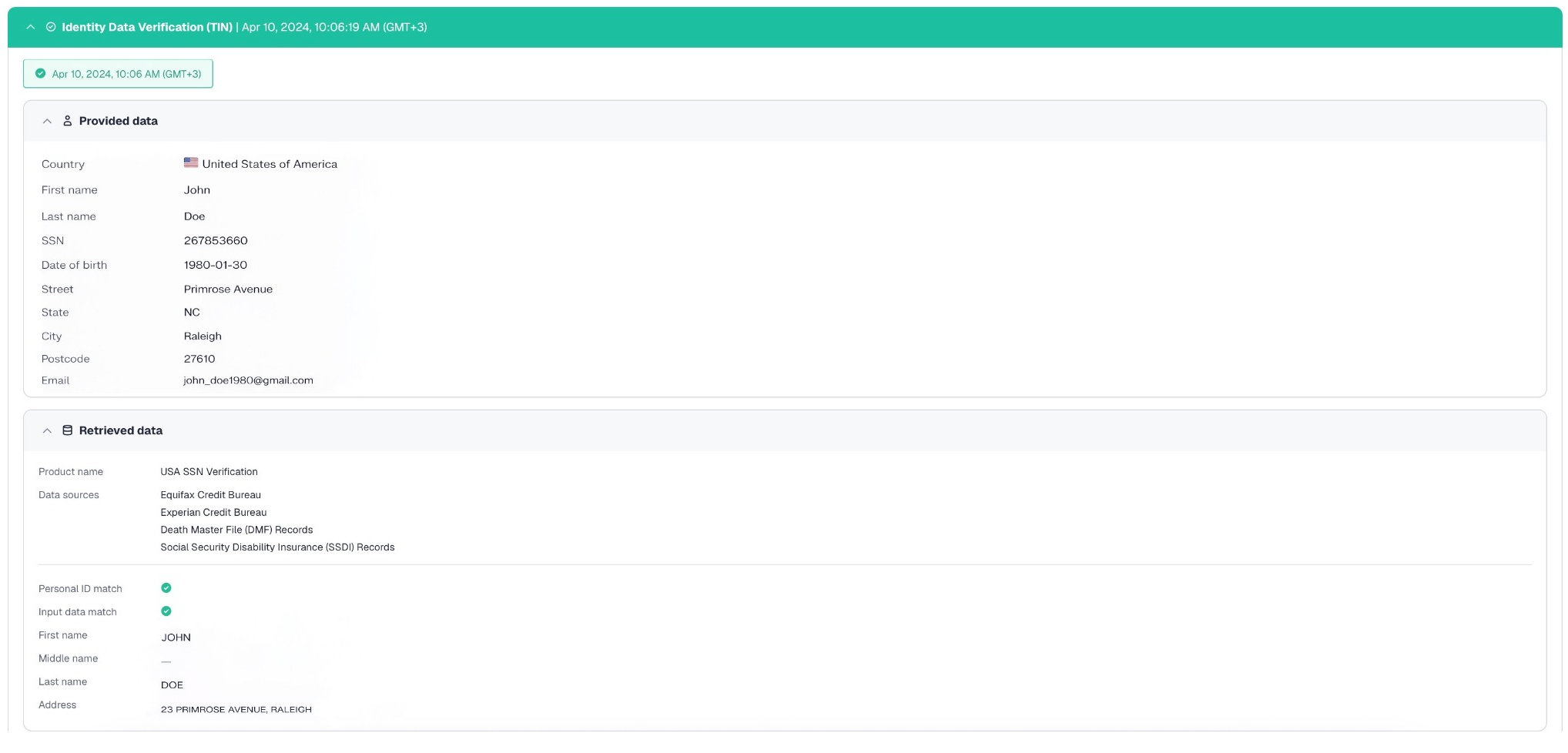
Identity Data Verification
Identity Data Verification indicates check results showing the reliability of the provided PoI documents:
- The Provided data section shows the data obtained from the trusted government and commercial sources by the applicant PoI document number.
- The Retrieved data section indicates the check status of the submitted document.
Based on the extracted data, we can confirm the validity of the submitted document:
- The green () check label means that the identity document is valid.
- The red () check label means that the document is invalid or it was not possible to extract the required data.
The timestamps that you can find next to the name of the check indicate the date and time when the given check was performed. They are also highlighted in the color corresponding to the check result.
Depending on the check results, the system assigns a label explaining the given status as per the following table.
|
Check label |
Check state |
|---|---|
|
Identity document is valid |
Green () — Provided document meets the required criteria for being issued by a recognized government authority, and is not expired. |
|
Lost |
Red () — According to the databases, the provided document is listed as lost. |
|
The identity document is incorrect |
Red () — Provided document contains errors or inaccurate personal information. |
|
Expired |
Red () — Document validity period has expired. |
|
Issued in violation |
Red () — Provided document was obtained through fraudulent means or in violation of the issuing authority's regulations. |
|
Seized, destroyed |
Red () — Provided document has been seized or rendered unusable by authorities. |
|
Technical defect |
Red () — Not possible to extract the required data due to damage that affects document integrity. |
|
This passport is invalid due to the owner's death |
Red () — Provided document belongs to another person who has passed away. |
|
Issue date is invalid |
Red () — The issue date on the identity document is incorrect or falls outside the valid time frame. |
|
Identity document not found |
Red () — Provided document was not found in the databases. |
|
Identity document data mismatch |
Red () — The information on the identity document does not match the information provided by the applicant. |
|
Identity document is suspended |
Red () — Provided document has been suspended or revoked by the issuing authority. |
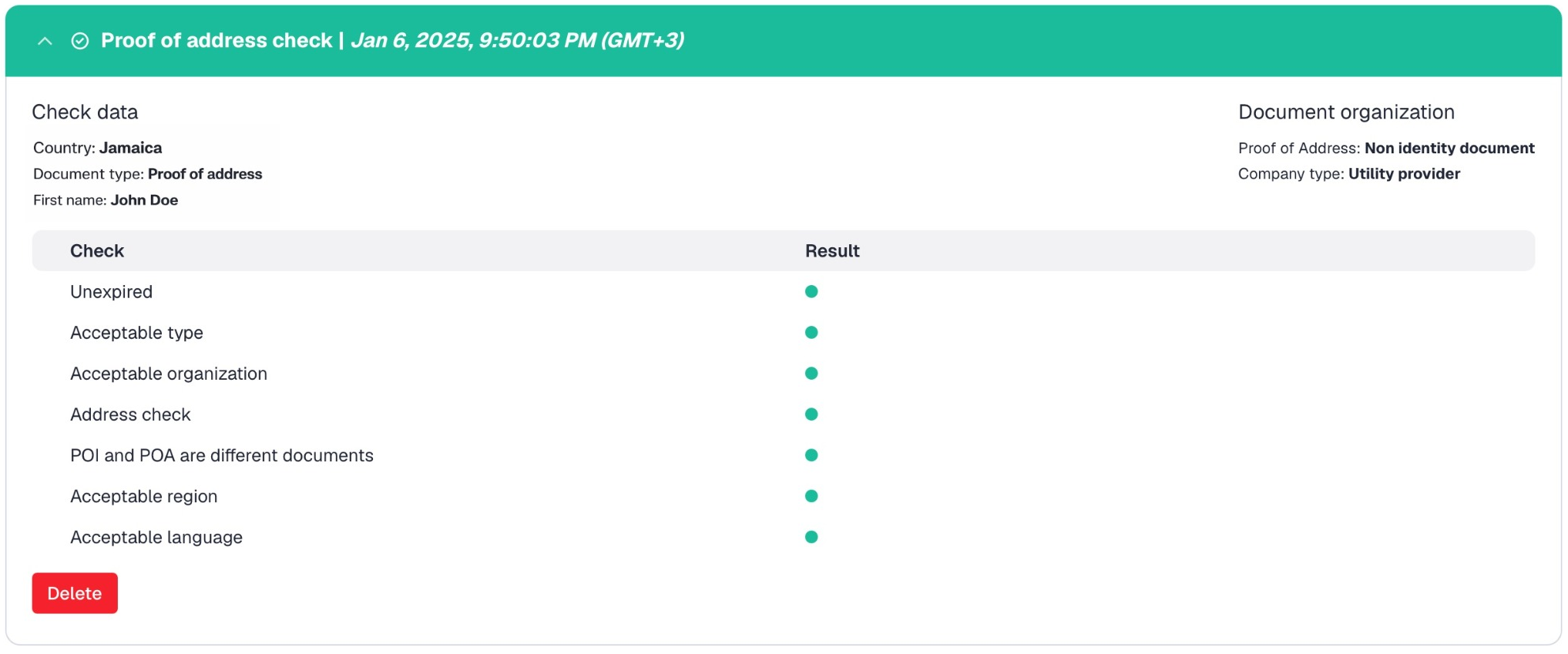
Proof of address check
Proof of address checks indicate check results showing the reliability of the provided PoA documents.
The results may include the following parameters:
- Layout and format
- Misaligned margins
- Misaligned tables
- Inconsistent spacing
- Unusual borders
- Incomplete or broken table rendering
- Different fonts in one document
- Different font sizes in one document
- Image quality
- Mixed sharpness when some parts of the image are clear, and some are blurred
- Cropped or pasted areas with visible edges or color differences
- Pixel noise around text
- Data Inconsistencies
- Lack of consistency of dates throughout the document
- Inconsistent language and localization
- Unrealistic billing amounts
The following table explains the check labels, their description, and possible check states as indicated by colors:
- The green () check label means that the identity document is valid.
- The yellow () check label means that it was not possible to extract enough data for a given check.
- The red () check label means that the address information is invalid.
|
Check label |
Description |
Check state |
|---|---|---|
|
Unexpired |
Indicates that the document is valid. |
Red () — The issue date or expiry date of PoA document does not match client settings. |
|
Acceptable type |
Shows whether the type or subtype of PoA document is acceptable. |
Red () — Type or subtype is forbidden by client settings or in case of ID as PoA, certain ID doc type is forbidden by client settings (for example — ID_CARD). |
|
Address check |
Shows whether the business address or PO box is acceptable. |
Red () — Business address or PO box is forbidden by client settings. |
|
POI and POA are different documents |
Verifies that PoI and PoA documents do not match. |
Red () — PoI and PoA are the same document, which is forbidden by client settings. |
|
Matches Proof of Identity country |
Indicates if PoI country matches with PoA country. |
Red () — PoI and PoA countries do not match. Gray () — Сheck is disabled in client settings. |
|
Acceptable region |
Verifies that the applicant address does not belong to disputed territories. |
Red () — PoA document contains the address of disputed territories. |
|
Acceptable language |
Reveals if PoA document contains languages forbidden by your settings. |
Red () — PoA contains languages forbidden by client settings. |
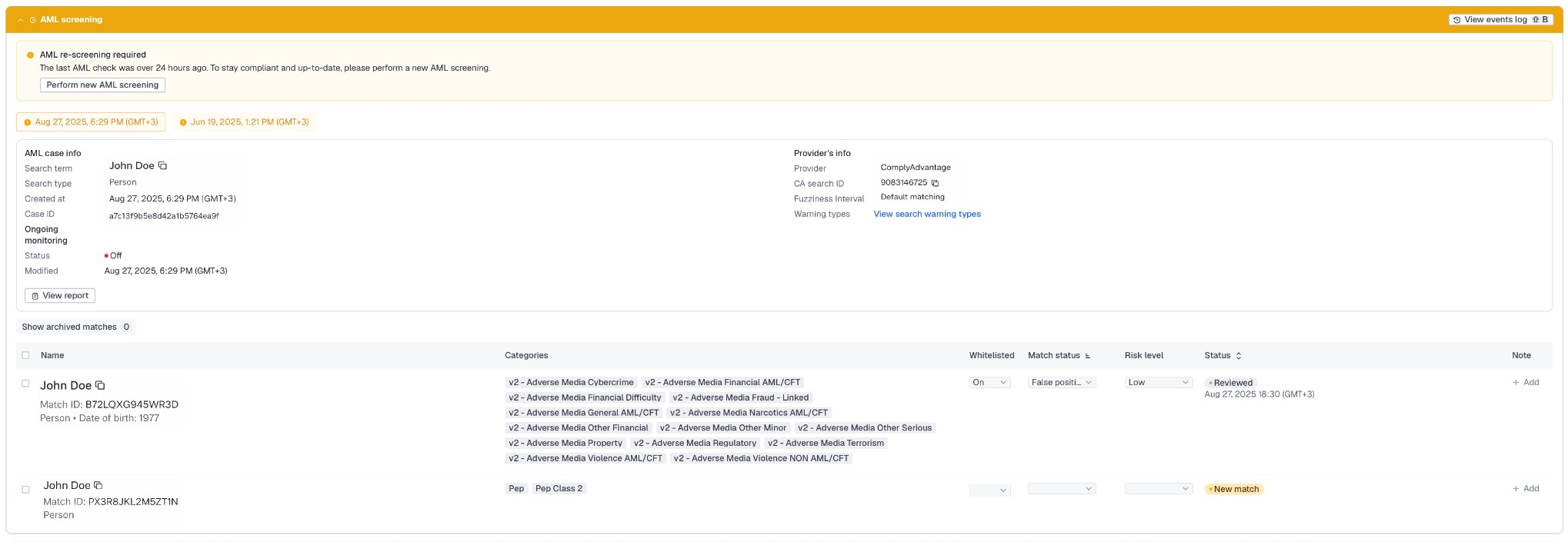
AML screening
During the auto-check, Sumsub uses the watchlist screening to determine if your applicants belong to any of the various sanction lists and watchlists across the globe.
The watchlist screening helps find applicants that are:
- Known or suspected terrorists
- Sanctioned persons
- Politically exposed persons (PEPs)
- Persons with criminal background
- Persons mentioned in adverse media
All applicants that belong to any of these categories are rejected automatically during the watchlists (WL) screening. To approve such applicants, follow the instructions given in this article.
To see everything that happens to an applicant’s AML screening check, you can view the AML screening events log.
You can also generate a screening report and save it as PDF.
Email and phone confirmation checks
Email and phone checks display the verification results that indicate the reliability of the provided email address and phone number.
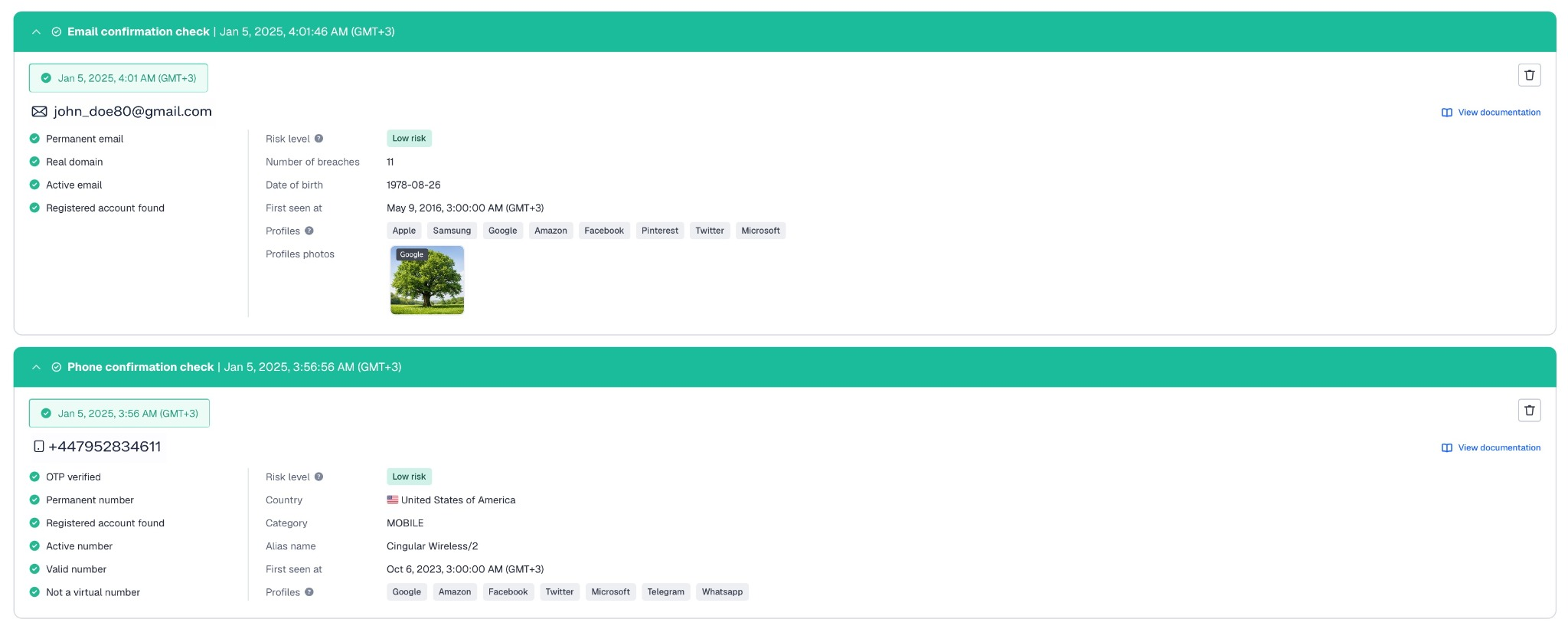
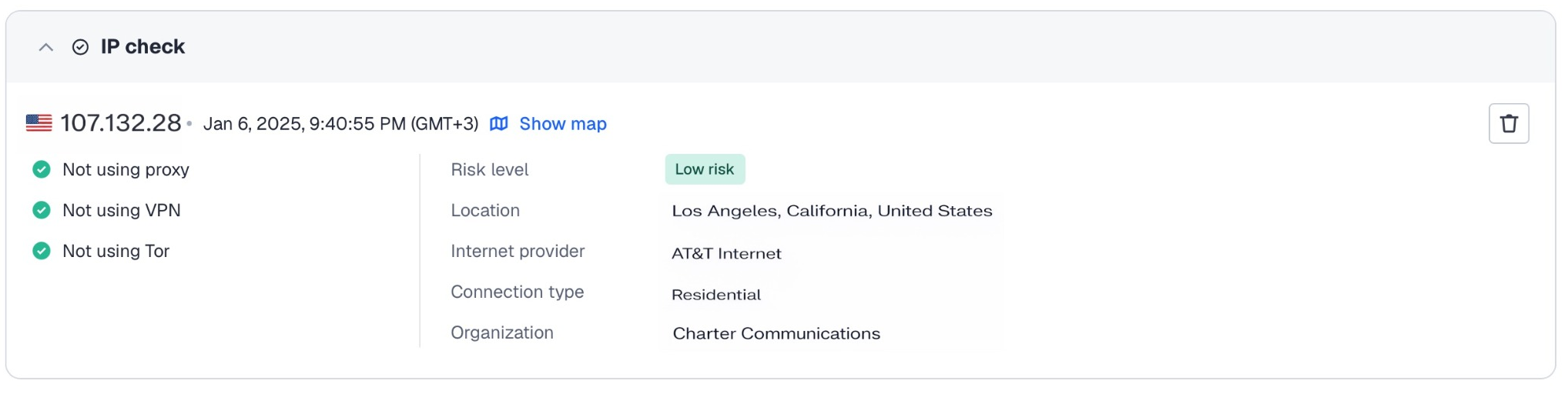
IP check
The IP check displays the verification results that indicate the reliability of the applicant's IP address used during verification.
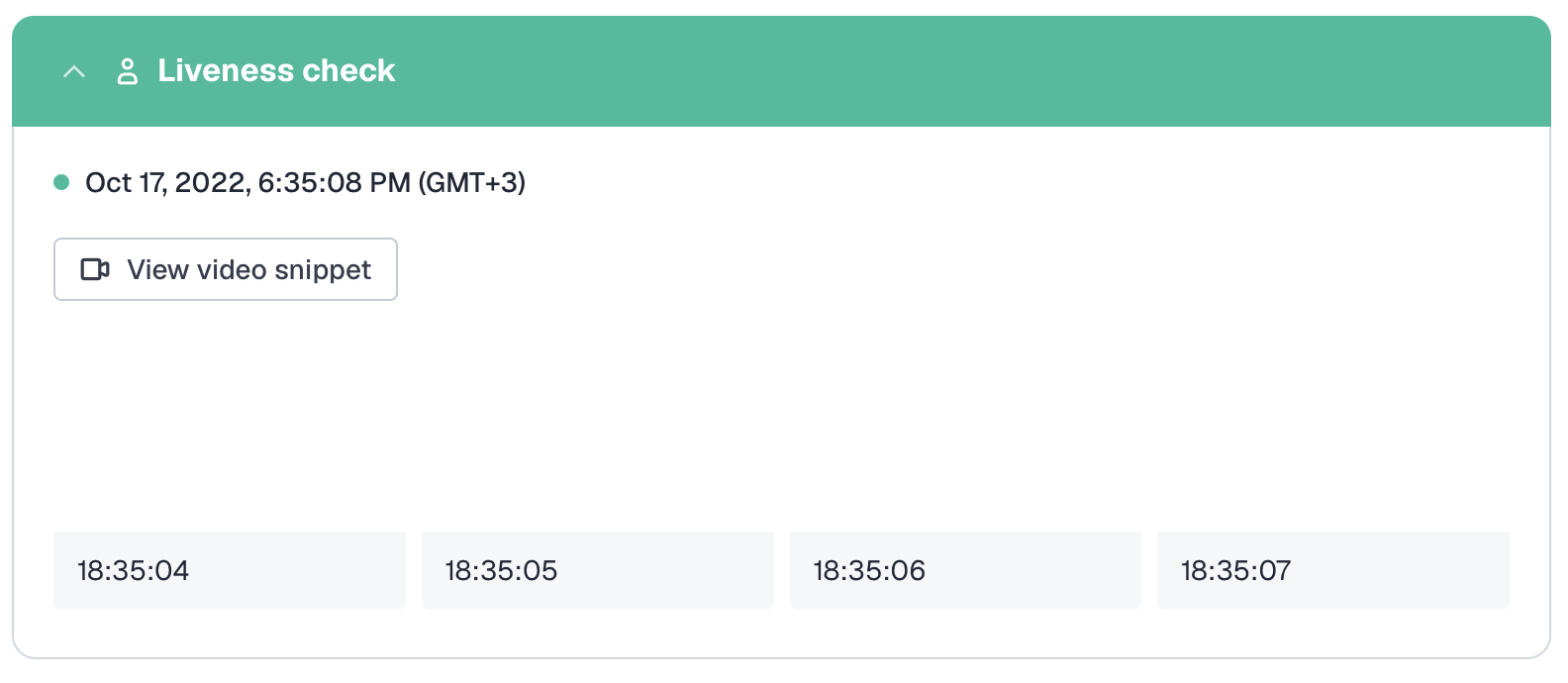
Liveness check
Liveness shows the results of the Liveness & Face match check passed by the applicant.
You can see such statistics as the date and time when the Liveness check was performed, information about the platform and device used during the Liveness session, view a video snippet, and pictures from the recorded selfie.
NoteThe Liveness check is performed only if the Selfie step (Advanced Liveness check) is added to the verification level.
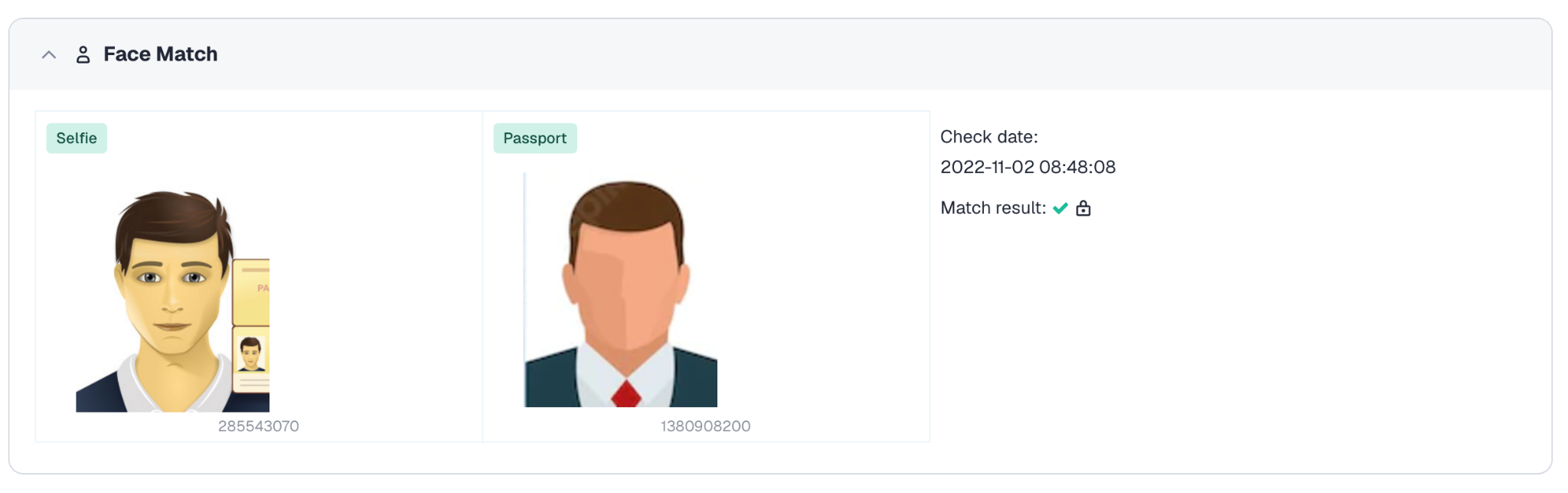
Face match
Face match displays the verification results that indicate whether the person in the identity document (PoI) is the same person presenting the selfie. The system does this by comparing facial representations extracted from both images.
Face match works in the following way:
- Face localization. The system identifies the portrait on the identity document using a database of known document templates (for example, passports, ID cards, driver’s licenses). This allows it to determine the face location for each document type and use the correct image region for further processing.
- Face detection and alignment. The document image and the selfie are processed to detect the face and align it into a consistent format. This step accounts for differences in orientation, scale, and lighting conditions.
- Feature extraction. Each detected face is converted into a numerical representation (embedding or feature vector). These vectors capture patterns learned from large datasets and encode the identity of a person for comparison.
- Face comparison. The embeddings from the document image and the selfie are compared to evaluate whether they correspond to the same identity. This comparison is based on overall similarity rather than any single feature.
- Face match result. The system determines whether the two images correspond to the same person. The result is a match or no-match outcome, displayed on the applicant page and used in the identity verification process.
Duplicates
Shows duplicate profiles.
To detect duplicates, Sumsub searches for profiles that have the same full name, ID documents, email addresses, phone numbers, or even facial features.
For more information on how to configure duplicate processing, see this article.
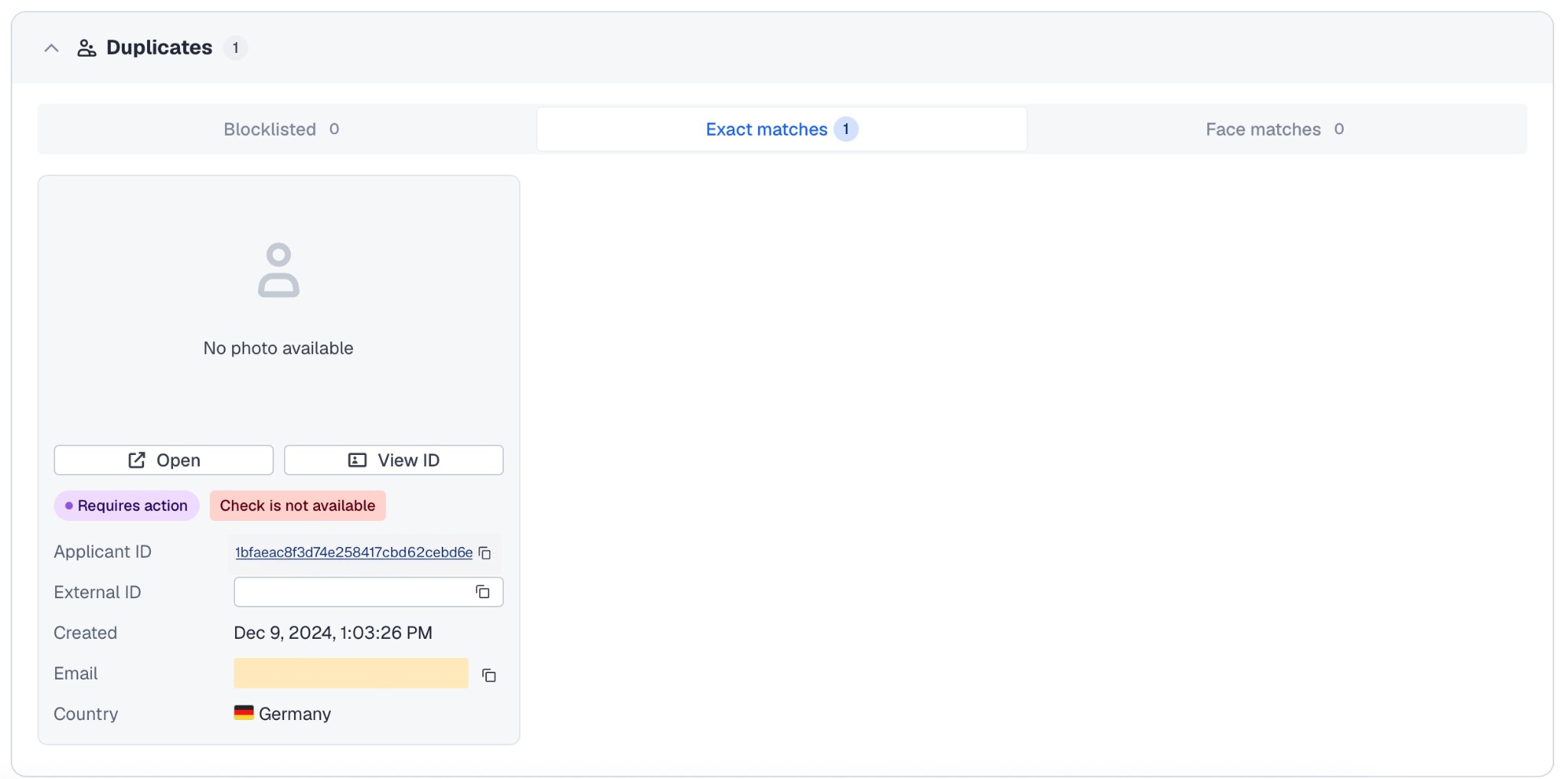
Face matches
The Face matches tab shows applicants whose selfie images look similar to the current applicant’s selfie, but whose profile data differs.
Sumsub searches for visually similar faces among applicants created under the same client key. This helps detect cases where the same person may use different identity data, change document data, or try to pass verification with someone else’s documents.
Applicants in this section are not necessarily exact duplicates. A face match means that Sumsub detected visual similarity between selfies, while the applicants have different text data in their profiles. Because of this, the section may include approved applicants who look similar to the current applicant but represent a different profile.
Review the matched applicants and compare their personal data, documents, selfies, and check results before making a decision.
NoteThe Face matches section appears only when face search is enabled for your account. If this service is not enabled, Sumsub does not search for visually similar applicants and the section remains empty.
To enable face similarity search, contact your Customer Success Manager or our support team.
Photos
The Photos section contains a list of documents submitted by applicants during verification in accordance with the verification level settings.
For example, you may want to request applicants to submit identity documents, such as a passport, driver's license, or resident permit, along with some additional proof of identity, such as the second identity document (for example, student ID or vehicle passport) and/or residence permit, and so on.
Each of the documents submitted by your applicants is listed independently, one after another, showing its verification status and rejection reasons (if any).
You can perform the following actions on documents:
- Change the current status of any document if needed.
- Edit document information in case the OCR engine could not recognize it properly.
- Change document information, such as its country and type, and remove the document.
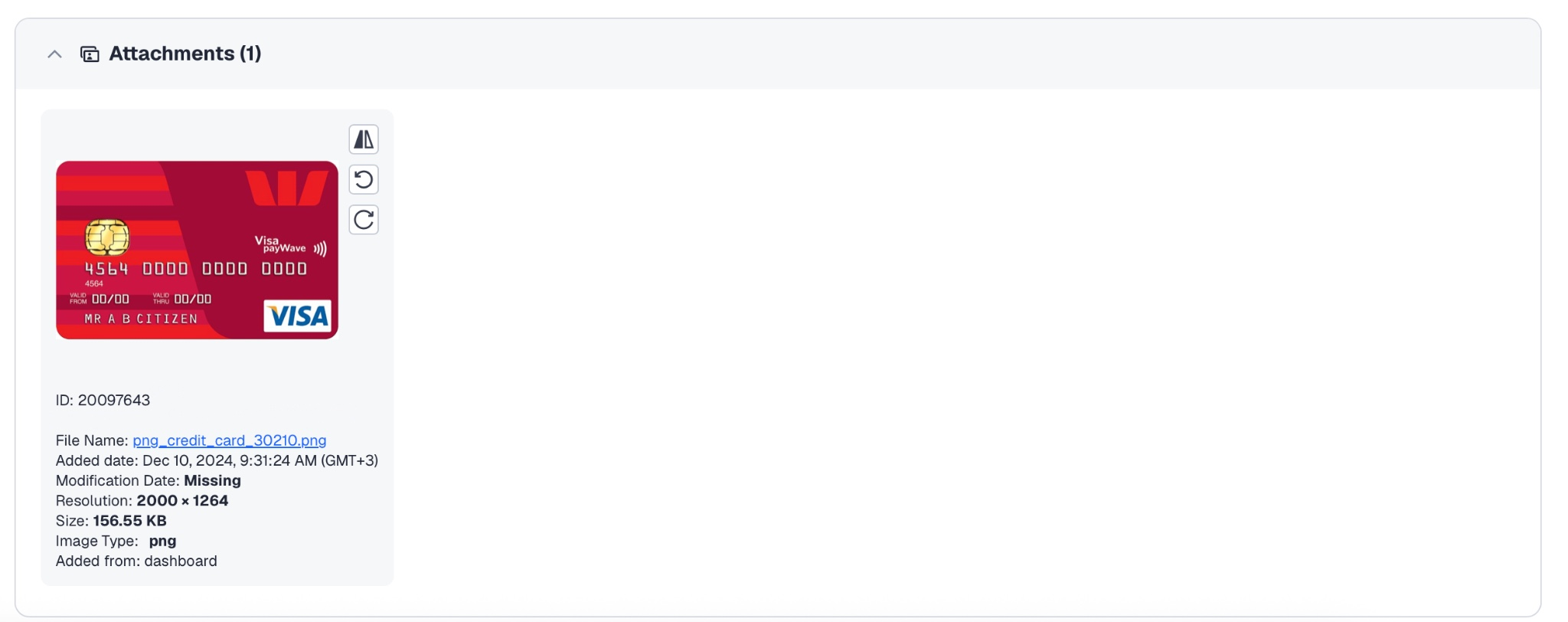
Attachments
In the Attachments section, the applicant can upload specific documents that were not included in the standard set of documents for certain checks. You can use such documents on other stages.
For example, the applicant needs to complete the questionnaire with a particular document, such as Form W8-BEN, and provide a Water Bill. It can be marked as a PoA document, but we do not request it during the regular PoA check.
Updated 1 day ago